1 min read
Why Building Digital Trust Matters for Nonprofits
The digital world can be a scary place. We are constantly bombarded with news stories about cyber breaches and data leaks. It's easy to feel like our...
2 min read
 Joshua Peskay
:
Jun 3, 2022 3:37:39 PM
Joshua Peskay
:
Jun 3, 2022 3:37:39 PM

The Verizon Data Breach Investigation Report (DBIR) is one of the most comprehensive studies on data breaches in the world. Every year, Verizon releases a report that analyzes data from thousands of breaches across dozens of industries. The goal of the report is to help organizations improve their security posture and protect themselves against future attacks. In this blog post, we will summarize the key findings from the 2022 DBIR report.
Here is the simple version of what is going on in the world according to the 2022 DBIR
Credentials and Phishing are, BY FAR, the most commonly exploited vulnerabilities.
"There are four key paths leading to your data & money: Credentials, Phishing, Exploiting vulnerabilities, and Botnets. These four pervade all areas of the DBIR, and no organization is safe without a plan to handle them all.”
“Ransomware has continued its upward trend with an almost 13% increase–a rise as big as the last five years combined."
It’s important to remember that ransomware by itself is really just the most popular model of monetizing cyber attacks. Ransomware is not how cybercriminals breach your defenses, ransomware is what they do after they breach your defenses.
“The human element continues to drive breaches. This year 82% of breaches involved the human element. Whether it is the Use of stolen credentials, Phishing, Misuse, or simply an Error, people continue to play a very large role in incidents and breaches alike.”
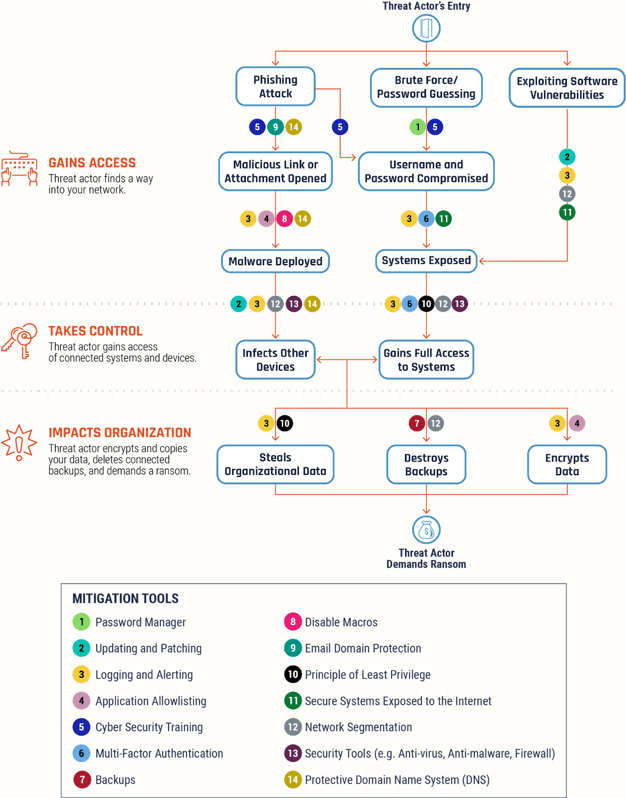
The Canadian Centre for Cybersecurity released a “Ransomware Playbook” in November of 2021. The entire playbook is a great resource, but I’m excerpting two visuals here. The first breaks down the workflow from the attacker (threat actor) perspective. The second is the same workflow but with the indicated mitigations (cybersecurity practices) in place. It shows both how attackers get into your environment, explore and analyze, establish footholds, and ultimately prepare and launch ransomware attacks. Understanding this workflow can help you understand how the different mitigations all help disrupt the attacker at various stages of the workflow. This also underscores the importance of a “defense in depth” strategy.
Source: Ransomware playbook (ITSM.00.099) - Canadian Centre for Cyber Security
Source: Ransomware playbook (ITSM.00.099) - Canadian Centre for Cyber Security
There are a few key takeaways from the 2022 DBIR report that organizations can use to improve their security posture.
The annual Verizon Data Breach Investigations Report is a must-read for any organization that is serious about protecting its data. By understanding the biggest threats and trends, organizations can take steps to improve their security posture and protect themselves against future attacks.
Did you find this blog post helpful? Share it with your network! And don’t forget to check out our other blog posts for more great content.

1 min read
The digital world can be a scary place. We are constantly bombarded with news stories about cyber breaches and data leaks. It's easy to feel like our...

1 min read
In a world where data breaches are becoming increasingly common, cybersecurity insurance is a must for any organization that stores or processes...

1 min read
As of December 22, 2022, LastPass announced a recent cybersecurity incident and many RoundTable customers have asked what this means for them.